The modern Internet had its beginnings in 1969 as the US military-sponsored ARPANET, initially connecting only three universities and a research institute.
Since then, the Internet has grown to cover the entire world; it connects everything from hand-held devices to refrigerators to industrial equipment, and virtually everything in between. The term “Internet of Things” has been coined to describe the phenomenon of a world filled with Internet-connected devices. The Internet of Things, or IoT, presents many opportunities for streamlining and simplifying tasks, whether professional or personal. But the IoT could also propagate unprecedented dangers due to widespread software vulnerabilities. The dangers posed by an unsecured IoT constitute a real threat to national security and to the civilian populace. This threat may only be countered by the development and adoption of consistent industrial and governmental security standards.
The Components of the IoT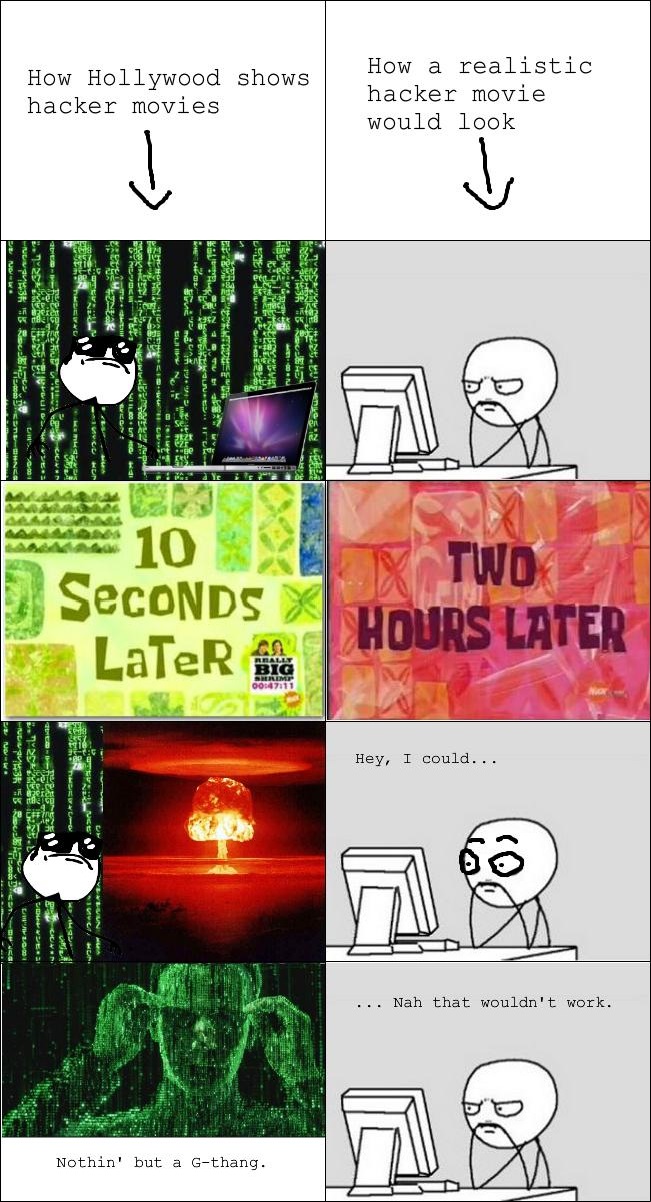
The IoT includes a virtually limitless repertoire of Internet-connected devices that may be tracked, catalogued, monitored, controlled, or managed via the Internet:
- Personal devices (phones, tablets)
- Visual media devices (TVs, game consoles, etc.)
- Home infrastructure, such as refrigerators, clothes washing machines, lighting systems, and more
- Medical infrastructure, both in hospitals and portable monitoring systems
- Industrial and manufacturing infrastructure
- Transportation devices, including cars, airplanes, and more
- Security systems, both industrial and for the home
These connected, “smart” devices offer businesses and individual users abilities they have never had before. For example, users can control their all of their IoT appliances from a single smartphone. Businesses have access to detailed metrics and data on every single customer.
Hollywood’s Half-Truths
Many people are concerned about the risks inherent in an overwhelming integration of software into everyday life. The theme of software threatening ordinary people has pervaded popular culture in recent decades. Movies and TV shows often play on the common fear that software could be either rigged or hijacked to harm the populace.
- The television episode Doctor Who: The Sontaran Strategem features a world dominated by “smart cars” which are designed to kill their unsuspecting drivers and aid in an alien takeover.
- In the TV show Person of Interest, a computer hacker designs an artificial intelligence system that can hack into worldwide Internet-connected infrastructure to spy on everyone and predict their actions with incredible accuracy.
- In the movie Terminator Genisys, a new phone operating system that allows every device to “seamlessly connect” turns out to be part of a plot to control the populace.
While these shows are fictional and meant for entertainment purposes rather than for serious consideration, they represent a common and compelling belief, that the pervasion of the Internet of Things can become a threat if it is misused or poorly designed.
Real-Life Dangers
In fact, the vulnerabilities of the Internet of Things are not purely fictional: there have been a number of disturbing or life-threatening incidents caused by deficiencies in IoT infrastructure. In the late 1980s, a computerized radiation treatment system called Therac-25 contained malfunctioning software. It caused at least six accidents that resulted in serious injury or death to cancer patients.1 In 2005, software bugs in Prius Hybrid cars caused the vehicles to stall or even shut down while driving at highway speeds.2 The widely publicized Heartbleed vulnerability, discovered in April 2014, compromised the security of an estimated 20% of the entire Internet.3 Even more recently in February 2016, software security researchers discovered a bug in a software package called “glibc” that rendered more than half of all Internet-connected devices potentially vulnerable to certain types of attacks.4
The recent vulnerabilities in certain Chrysler automobile systems are an excellent case study in the potential threat posed by the IoT. In July 2015, two security experts revealed a vulnerability in new Chrysler “smart” vehicles with Uconnect technology that would allow hackers to take over control of such cars remotely. After hacking into a Uconnect-equipped Chrysler vehicle, the security experts demonstrated that they could replace the vehicle’s firmware, remotely start the engine, accelerate, steer, and brake. When the vulnerability was found, an estimated 471,000 of such vehicles were on the road.5 The bug was quickly fixed, but if malicious hackers or terrorists had discovered it first, the threat would easily have been large enough to be considered a national security threat.
Government Action: It’s Easy to Talk
The US government has already begun to take action in an attempt to secure the IoT. Senators Markey (D-MA) and Blumenthal (D-CT) are working on legislation that would mandate certain security standards for all Internet-connected vehicles. The National Security Telecommunications Advisory Committee estimated in 2014 that in fewer than five years, it would be too late to protect the IoT, and that “[i]f the country fails to [secure the IoT], it will be coping with the consequences for generations.”6
Unfortunately, while it is easy to form committees that mandate secure software, it is much more difficult on any practical level to ensure that software is entirely hacker-proof. Due to human error, the tendency to create vulnerabilities in software seems unavoidable. As illustrated by the recent Heartbleed and glibc vulnerabilities, even highly-vetted software in use for extended periods of time may contain vulnerabilities that simply go unnoticed. While a focus on good security practices certainly helps improve software security, it is nearly impossible to stamp out software vulnerabilities altogether.
Dangerous When Fully Grown
Right now, due to the nature of software development, it is unlikely that terrorists could take over the entire IoT and use it to threaten the populace. The IoT is not a homogenous entity to be hacked in one fell swoop. In order to perform a coordinated attack on civilian and government infrastructures, hackers would need to rely on uniform vulnerabilities across the range of IoT devices and intimate knowledge of thousands of interoperable but unique systems. Because software is constantly changing and updating, the IoT is a fast-moving target. Secure systems do exist. The idea that all computer systems are universally hackable is largely a Hollywood myth.
However, the number of years that device heterogeneity can be relied on as a security measure is in the single digits. As the IoT grows in number and scope, it would be a grave mistake to ignore security concerns. Water, power, health care, transportation, industrial infrastructure, and interpersonal communications have all become increasingly dependent on the IoT. Any number of these systems has the potential to become compromised. As the IoT grows, so must the reliance on industrial and governmental standards of security: “The devices coming are very different from traditional PCs and servers. [These IoT devices] will face new barriers to success if manufacturers don’t increase their level of attention to security and if enterprise security processes and controls don’t evolve.”7
Fortunately, the technology industry has already recognized its unique responsibility to secure IoT devices. Widespread software vulnerabilities are not just bad for national security—they are bad for business as well. Thanks to so-called hacker-activists (or “hacktivists”), glaring software vulnerabilities often get excellent press coverage, pressuring developers into quickly patching the vulnerabilities in their software. The software development sector has been rapidly evolving to face the challenge of maintaining a secure IoT that will protect both civilian and national security interests.
The Internet of Things is not a harbinger of doom, but neither is it entirely reliable or secure. Every Internet-connected device effectively becomes part of the IoT, and manufacturers must realize the implications of this. As the industry evolves, it is important for the government and tech industries to work together to develop effective and consistent security vetting procedures for all IoT devices. The IoT is still in its infancy; it must be secured before it fully matures. ■
- Nancy Leveson and Clark S. Turner, “An Investigation of the Therac-25 Accidents,” Virginia Tech, July 1993, http://courses.cs.vt.edu/~cs3604/lib/Therac_25/Therac_1.html.
- “Prius hybrids dogged by software,” CNN Money, 16 May 2005, http://money.cnn.com/2005/05/16/Autos/prius_computer/index.htm?cnn=yes.
- “The Heartbleed Bug,” Codenomicon, April 2014, http://heartbleed.com/.
- Dan Goodin, “Extremely severe bug leaves dizzying number of software and devices vulnerable,” Ars Technica, 16 February 2016, http://arstechnica.com/security/2016/02/extremely-severe-bug-leaves-dizzying-number-of-apps-and-devices-vulnerable/.
- Andy Greenberg, “Hackers Remotely Kill a Jeep on the Highway—With Me in It,” Wired, 21 July 2015, http://www.wired.com/2015/07/hackers-remotely-kill-jeep-highway/.
- Jack Moore, “Report: Government Has Only 5 Years to Secure Internet of Things,” Nextgov, 19 November 2014, http://www.nextgov.com/cybersecurity/2014/11/report-government-has-only-5-years-secure-internet-things/99446/.
- John Pescatore, “Securing the Internet of Things Survey,” SANS Institute, January 2014, https://www.sans.org/reading-room/whitepapers/analyst/securing-internet-things-survey-34785.
Spring 2016
Volume 18, Issue 1
16 February