It's all fun and games until terrorist start planning attacks in online gaming lobbies
Which sounds more preposterous: detailing the plans for the next massive terrorist attack on a virtual wall in a Call of Duty® (CoD) multiplayer match,; or known terrorists transferring money to each other over League of Legend® (LoL) servers? Both sound crazy. Yet several world leaders have identified gaming servers as potential exploitation tools terror groups use to conduct operations abroad. Gaming servers utilize communication and financial encryption protocols prevent fraud and user impersonation. However, the same protocols than enable online security allow nefarious actors to operate covertly online. Federal governments have requested that gaming servers and other encrypted communication services offer “backdoor” access to encrypted content. While the threat of terror does not justify an Orwellian videogame surveillance state, the United States Intelligence Community should increase counterintelligence operations on gaming servers like League of Legends®, World of Warcraft®, PlayStation Network®, and Xbox Live®.
Online gaming is becoming an increasingly common phenomenon in modern society. As participation in virtual online systems increases, so does their potential to be used for illegal purposes. It is hard to find a young person in the West who does not participate in at least one form of online gaming. In 2016, more people watched the League of Legends® Worlds Championship than the NBA Championship. The final League of Legends® round at the Mercedes-Benz Arena in Berlin, Germany, garnered more than 36 million unique viewers.1 As the frequency of use of gaming platform increases, users will find more diverse ways to use them. Today, gamers pretend to go on quests together, destroy enemy nexuses, and work on building their kingdoms. Tomorrow, perhaps they will use these virtual realities to communicate stolen information and plan terrorist operations.
It’s All Fun and Games Until Someone Gets Hurt
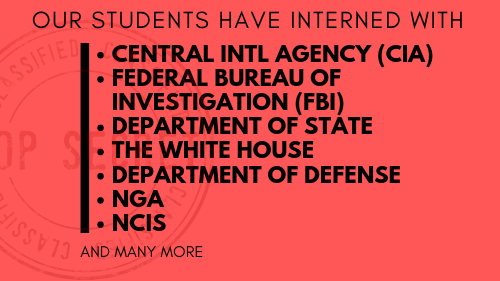
Federal governments have known about the potential threat imbedded in massive multiplayer online (MMO) games for several years. The US National Security Agency (NSA) and British Government Communication Headquarters (GCHQ) conduct routine counterintelligence operations in MMOs like World of Warcraft® and Second Life®.2 Agents from both the NSA and the GCHQ create characters in order to develop informants and monitor communications between players. These agencies utilize exploitation teams to extract data on user accounts, characters, and guild associations in an attempt to link users to Islamic extremist groups and organized crime networks. Intelligence agencies worldwide recognize the anonymous appeal of gaming servers like League of Legends®, World of Warcraft®, the PlayStation Network®, and Xbox Live®. Gamers have a virtual reality in which they can be anyone, talk with anyone, and give money to anyone – a terrorist’s paradise.
Plans for Terror
In response to the Paris terrorist attack in November 2015, Belgian raided several terrorist cells. In one of the raids, investigators found a PlayStation 4. This prompted Jan Jombon, Belgian’s Federal Home Affairs Minister, to explain the safety blanket that encryption provides terrorists.3 Communication over the PlayStation Network® is an easily accessible and more secure way for terrorists to communicate with each other. There are over 65 million active PlayStation users worldwide. The breadth of the communication network alone makes it almost impossible to monitor.3 In addition, terrorists have the option of talking to each other within specific title games like Call of Duty®, where they can create a multiplayer match and initiate voice/text chats that disappear as soon as the match is over.
Platform for Cybercrime
In recent years, cybercriminals have been very interested in online gaming. As video games have been increasingly used online, criminals have found ways to exploit systems and users. On Christmas Day, 2014, the infamous hacker group “Lizard Squad” downed Play Station Network® and Xbox Live® servers with massive DDoS attacks, presumably to ruin the holidays.4 In January 2015, Minecraft® login details were compromised, Valve’s Steam® accounts are constantly targeted, and VTech’s® gaming platform was attacked, resulting in the theft of millions of customer details.4 Cybercriminals use online gaming as a way to rake in funds, usually by stealing or selling user data or convincing users to give them their bank details. As big of a problem that theft of personal information presents, however, it does not compare to cybercriminals’ use of gaming platforms for money laundering.
League and Laundering
In June 2013, the United Nations Office on Drugs and Crime issued a report identifying online gaming as a major avenue for money laundering utilizing virtual economies in gaming systems.5 For instance, World of Warcraft® and League of Legends® – both massively played online games – feature systems where you can use real money in exchange for in-game currency. Cartel-related actors launder more than $7 billion every year through Colombian corporations and the Black Market Peso Exchange (BMPE). These dollars are used to buy traditional US goods and then sold back in Colombia. Cartel money launderers have augmented these efforts with web technologies, including black marketplaces and cryptocurrencies like gaming currency.6 Online gambling has also been widely used for money laundering. In 2012, 2,926 websites offered gambling products like casino games and customers could pay with up to 235 different payments methods, including credit cards, prepaid cards, bank wires, and player-to-player transfers.7 The online gambling market is worth more than $39 billion, and in October 2011 there were at least 25,000 unlicensed gambling sites.8 Online gaming and gambling provides the perfect opportunity for criminal and terrorist groups to covertly move money around the globe.
Necessity for Encryption
MMO games present the opportunity to terrorists and organized crime members to communicate and transfer money to each other under a blanket of encryption. However, that encryption deserves its place in gaming servers’ code. MMO gamers enjoy free speech on forums, the ability to pay to level up, and the right to expect that servers will protect their information. All gaming servers will have some vulnerabilities and will always be hackers roaming the global network exploiting those vulnerabilities.
League of Legends®, a recently popular MMO in which competitors select champions to fight against each other on a forested battlefield, experienced a massive security breach back in 2012. Hackers obtained usernames, e-mail addresses, passwords, and 120,000 credit card numbers.9 In the past five years, 3 different gaming producers – ZeniMax®, World of Warcraft®, and Ubisoft® – experienced similar attacks, compromising credit cards and user anonymity.9 These are just a few examples demonstrating the need for encryption on gaming servers. Vulnerabilities are inherent to any computer programming – online gaming is not an exception.
Counterintelligence Ops in MMOs
The U.S. government has to walk a tight line in balancing national security with respect to consumer expectation of privacy. Gaming developers have not yet granted the US Intelligence Community backdoor access to their encryption protocols. Regardless, the Intelligence Community should increase or initiate collection and counterintelligence operations in online gaming platforms like World of Warcraft®, League of Legends®, and the PlayStation Network®. Specifically, the Intelligence Community should include online gaming in its scope when applying the National Counterintelligence Strategy. This strategy aims to increase intelligence gathering while balancing privacy concerns. Integral to this plan is recognizing terrorist operators in virtual realities as legitimate foreign intelligence entities.
The U.S National Counterintelligence Strategy focuses on detecting, exploiting, and neutralizing foreign intelligence entity threats. The overall focus of the approach centers on integrating a public and private sector whole-of-government implementation of countermeasures to the threat environment. The strategy’s primary enabling objective is to “strengthen secure collaboration, responsible information sharing, and safeguarding effective partnerships.”10 Therefore, in accordance with this strategy, the US Intelligence Community ought to establish partnerships with major online gaming producers. These partnerships should primarily enable intelligence agencies to insert covert operatives into gaming lobbies and monitor account transactions without necessarily revealing the identity of the users themselves. ■
- “More People Watched League of Legends Than the Nba Finals,” Kotaku, http://www.kotaku.com.au/2016/06/more-people-watched-league-of-legends-than-the-nba-finals/.
- “The Nsa Tracks World of Warcraft and Other Online Games for Terrorist Clues,” Computerworld, http://www.computerworld.com/article/2486632/cyberwarfare/the-nsa-tracks-world-of-warcraft-and-other-online-games-for-terrorist-clues.html.
- “Online Gaming New Frontier for Cybercriminals,” Welivesecurity, http://www.welivesecurity.com/2015/12/24/online-gaming-new-frontier-cybercriminals/.
- “Laundering Money Onlin E: A Review of Cybercriminals’ Methods,”, accessed November 14, 2016, https://arxiv.org/pdf/1310.2368v1.pdf.
- “Money Laundering Online,” Wired, accessed November 14, 2016, http://www.wired.co.uk/article/money-laundering-online.
- “Online Gambling as a Game Changer for Money Laundering,” Wiso, accessed November 14, 2016, https://www.wiso.uni-hamburg.de/fileadmin/bwl/rechtderwirtschaft/institut/Ingo_Fiedler/Online_Gambling_as_a_Game_Changer_to_Money_Laundering_01.pdf.
- “Online Gaming the New Home for Money Launderers,” CNBC, 7. http://www.cnbc.com/2014/04/25/online-gambling-the-new-home-for-money-launderers.html.
- “League of Legends Is Hacked with Crucial User Info Accessed,” CNET, accessed https://www.cnet.com/news/league-of-legends-is-hacked-with-crucial-user-info-.
- “National Counter Intelligence Strategy,” National Security Council, https://www.ncsc.gov/publications/strategy/docs/National_CI_Strategy_2016.pdf.
Photo Credit:
Picture Edit @ Spencer Kolssak
Xbox Controller | https://static.pexels.com/photos/194511/pexels-photo-194511.jpeg
Spring 2017
Volume 20, Issue 5
17 May